Instructure's EduTech SaaS solution breach
ShinyHunters Strikes Again: The Instructure Canvas breach and what every organisation must learn
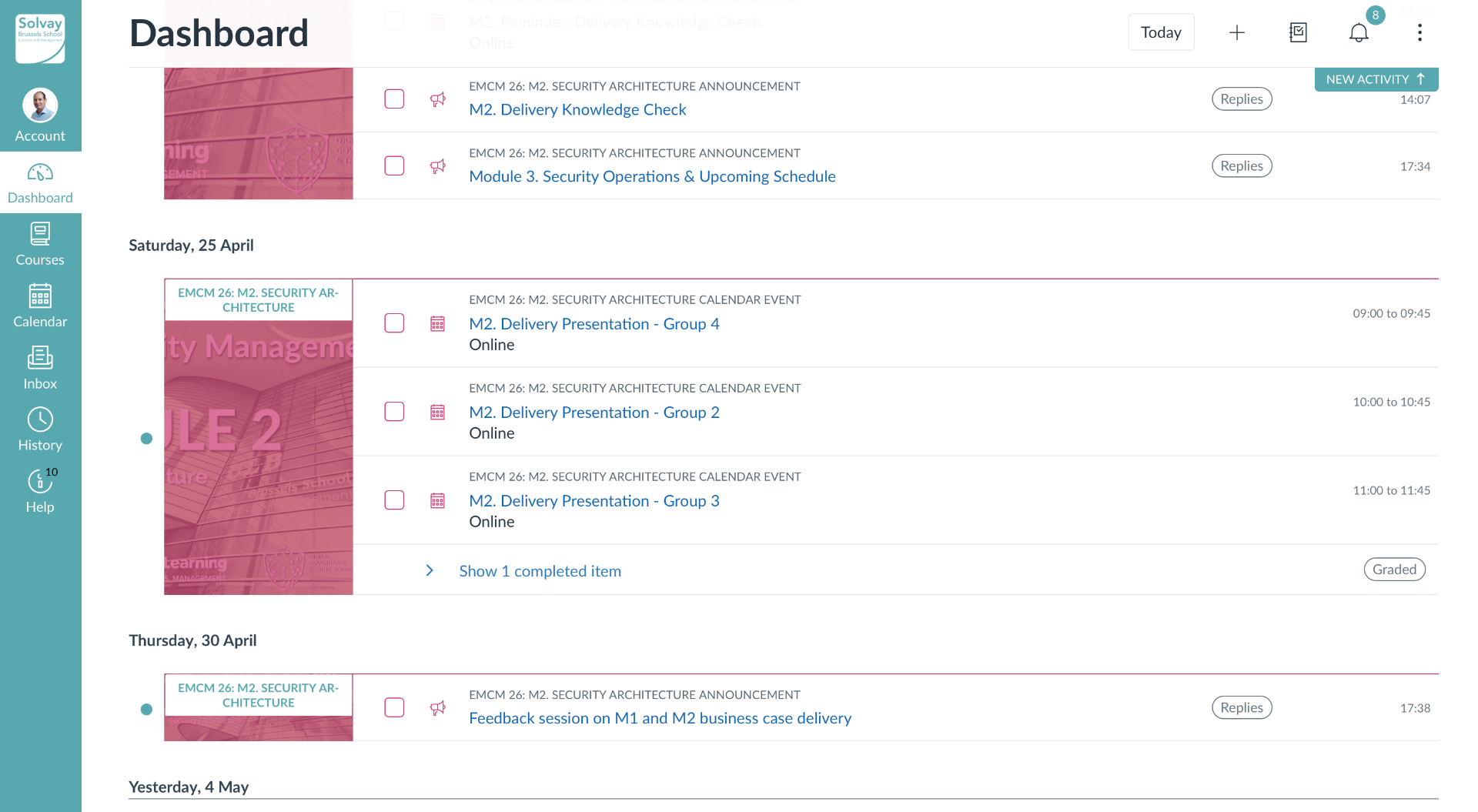
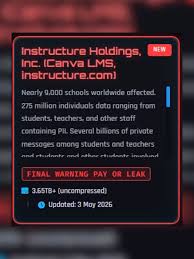
When Instructure — the Utah-based company behind Canvas, one of the world's most widely used Learning Management Systems — reported a "service interruption" on April 30, 2026, the language was deliberately understated. Within 72 hours, the truth had fully surfaced: a massive cyberattack had compromised the personal data of an estimated 275 million users across nearly 9,000 to 15,000 educational institutions globally. The threat actor? ShinyHunters — the notoriously persistent extortion gang that has been on a tear across enterprise SaaS environments for the past two years.
The Anatomy of the attack
Instructure confirmed on May 1 that cybercriminals had gained unauthorised access to its systems. The compromised data includes names, email addresses, student ID numbers, and — most alarmingly — private messages exchanged between students, teachers, and staff. ShinyHunters claims to have exfiltrated 3.65 terabytes of data, including "several billions of private messages" and data from Instructure's Salesforce instance. On May 3, the gang published the data on their Tor-based leak site, leaving virtually no ambiguity about the scale of the incident.
Instructure's response was operationally swift: API keys were rotated, privileged credentials were revoked, patches were deployed, and monitoring was enhanced. The company stated that passwords, dates of birth, government identifiers, and financial data were not part of the breach — a thin silver lining given the magnitude of the exposure.
This was not a surprise — it was a pattern
What makes this breach particularly damning is that it is not a first offence. In September 2025, ShinyHunters compromised Instructure's Salesforce environment via a social engineering attack. At the time, the company insisted no Canvas product data was accessed and downplayed the incident as involving "largely publicly available business contact data". That statement now reads as catastrophically premature. The threat actor had already mapped Instructure's environment, identified dependencies between its Salesforce instance and Canvas infrastructure, and likely used that initial foothold to plan this far larger intrusion.
This is a textbook example of progressive compromise — attackers do not always detonate the entire payload on the first access. They probe, escalate, and return. Organisations that treat a resolved first incident as a closed chapter, rather than a signal of persistent adversary interest, are setting themselves up for exactly this scenario.
A first technical analysis
While Instructure has not disclosed the specific vulnerability exploited, several indicators point to a SaaS integration attack surface. The disruption to "tools relying on API keys" — noted in the April 30 disclosure — suggests the attackers may have targeted OAuth tokens or third-party integration credentials that bridge Canvas with external platforms. The simultaneous compromise of the Salesforce instance reinforces this hypothesis: attackers likely moved laterally between integrated SaaS environments using stolen or forged API credentials, rather than attacking the Canvas core infrastructure directly.
This is consistent with ShinyHunters' known modus operandi. The group has historically combined social engineering with credential abuse across SaaS environments, exploiting the implicit trust that exists between cloud-hosted platforms and their integrated toolchains.
The scale — 3.65 TB of data involving billions of messages — also suggests that data exfiltration was likely slow-rolled over weeks or months, evading threshold-based detection. Instructure's confirmation that it needed outside forensics experts further indicates the attack was sophisticated enough to require reconstruction of the full timeline.
Lessons for every organisation running Ssimilar infrastructure
Any organisation running a multi-SaaS architecture — particularly one combining a core platform (like an LMS or ERP) with CRM tools like Salesforce — must draw concrete lessons from this incident:
- Treat integrated SaaS credentials as crown jewels. OAuth tokens and API keys connecting platforms are high-value targets; rotate them regularly and monitor them for anomalous usage patterns
- Never close a security incident without a full adversary-eviction assessment. The September 2025 Salesforce breach should have triggered a thorough review of all integration points — it did not
- Implement zero-trust between your own SaaS environments. Just because two tools are "yours" doesn't mean they should trust each other implicitly; apply least-privilege access between integrated platforms
- Log and monitor inter-system API traffic. Lateral movement between SaaS tools is invisible without dedicated observability across your integration layer
- Enforce message-level data classification. Private communications in educational or enterprise platforms carry significant PII risk and should be subject to dedicated access controls and DLP policies
The NIS2 Supply Chain dimension
For European organisations — schools, universities, public sector bodies — relying on Canvas as a critical third-party digital service, this breach is a live case study in the supply chain risk that NIS2 was explicitly designed to address.
Article 21 of the NIS2 Directive requires covered entities to implement risk management measures that explicitly account for the security of ICT supply chains and third-party service providers. NIS2 mandates a continuous, all-hazards approach: not just assessing a supplier at onboarding, but monitoring them on an ongoing basis, enforcing contractual security obligations, and having incident response procedures that activate when a key supplier is breached.
The Instructure breach should trigger, for any NIS2-covered institution using Canvas, an immediate supply chain risk reassessment: Is your Canvas integration exposing data beyond what is necessary? Are your API connections scoped with least privilege? Do your contracts with Instructure include breach notification SLAs and audit rights?
NIS2 also makes clear that ignorance of a supplier's security posture is not a defence. With ShinyHunters having publicly targeted Instructure twice in eight months, a covered entity that failed to reassess its risk exposure after the September 2025 incident faces a difficult conversation with its national supervisory authority.
The Instructure breach is not just an edtech story. It is a warning signal for every organisation that has wired its operations to a cloud-hosted SaaS platform — and assumed that the vendor's security is someone else's problem.